What Is Digital Identity Management (And Why It Matters Now)
Digital identity management is the set of processes and technologies used to create, maintain, secure, and govern the digital identities of people, devices, and applications across an organization’s systems. In the modern enterprise, this is no longer just a security requirement; it is a foundational element of digital strategy and brand trust.
Here’s a quick breakdown of what that means in practice:
- What it covers: Authentication, authorization, identity lifecycle management, access governance, and compliance.
- Who it applies to: Employees, customers, citizens, IoT devices, APIs, and software applications.
- Why it matters: It is the foundation of every secure interaction in a digital system. If you cannot verify who or what is accessing your resources, you cannot protect them, nor can you provide the seamless user experience that modern SEO and digital marketing demand.
More than half of organizations (51%) now rank managing and securing digital identities among their top three priorities, according to the Identity Defined Security Alliance.
That number makes sense when you look at the threat landscape. In Switzerland alone, cybercrime jumped 31% in 2023, with phishing attacks up nearly 70% and identity misuse surging over 66%. These aren’t isolated statistics; they reflect a global pattern where identity is the primary attack surface. For large companies, a single identity breach can lead to catastrophic data loss, regulatory fines, and a permanent decline in search engine visibility due to lost consumer trust.
At its core, a digital identity is a collection of unique attributes that represent an entity in the digital world. Think login credentials, biometric data, device fingerprints, or cryptographic keys. These attributes are what systems use to verify who you are and decide what you’re allowed to do. For large-scale organizations, managing these attributes across millions of users requires a sophisticated, automated approach to ensure both security and performance.
But digital identity is bigger than a single login or account. One person can hold multiple digital identities across different platforms. A single identity can span multiple accounts. And identities don’t belong only to humans — machines, apps, and IoT devices all have them too. Managing all of that, securely and at scale, is what digital identity management is really about.
I’m Chris Robino, a digital strategy leader with over two decades of experience helping organizations — from startups to global enterprises — navigate complex technology landscapes. My work focuses on the intersection of AI, security, and digital identity management. In this guide, we’ll walk you through everything from core concepts to emerging trends, including how identity management serves as a critical pillar for enterprise SEO and organizational growth.
Digital identity management terms at a glance:
The Core Pillars of Digital Identity Management
To master digital identity management, we first need to look at the framework that holds it all together. This is often referred to as Identity and Access Management (IAM). It isn’t just a piece of software; it’s a comprehensive framework of policies and technologies designed to mitigate risk while enabling business agility.
The primary goal is to ensure the right entities have the right access to the right resources at the right time. We achieve this through several core pillars:
- Identity Governance: This involves the “who has access to what” oversight. It ensures that access rights are granted according to business policy and regulatory requirements, providing the audit trails necessary for compliance.
- Provisioning: This is the process of creating a digital identity and granting it the necessary permissions. In large companies, this must be automated to handle high volumes of onboarding and offboarding.
- Access Control: Once an identity exists, we must control its movements. This is where we apply the principle of least privilege, ensuring a user only has the minimum access necessary to perform their job functions.
- Activity Monitoring: We don’t just “set it and forget it.” Continuous auditing and monitoring allow us to detect suspicious activities, such as credential stuffing or lateral movement, maintaining a high security posture.
A major part of modern strategy is moving toward a zero-trust model. In a zero-trust environment, we assume that no entity—inside or outside the network—is automatically trusted. Every request for access must be verified, which is essential for protecting the high-value digital assets that drive enterprise SEO and brand authority.
For those looking for the gold standard in technical frameworks, the NIST SP 800-63-3 Digital Identity Guidelines provide a foundational roadmap for managing these risks.
Understanding the Differences: Identity, Account, and User
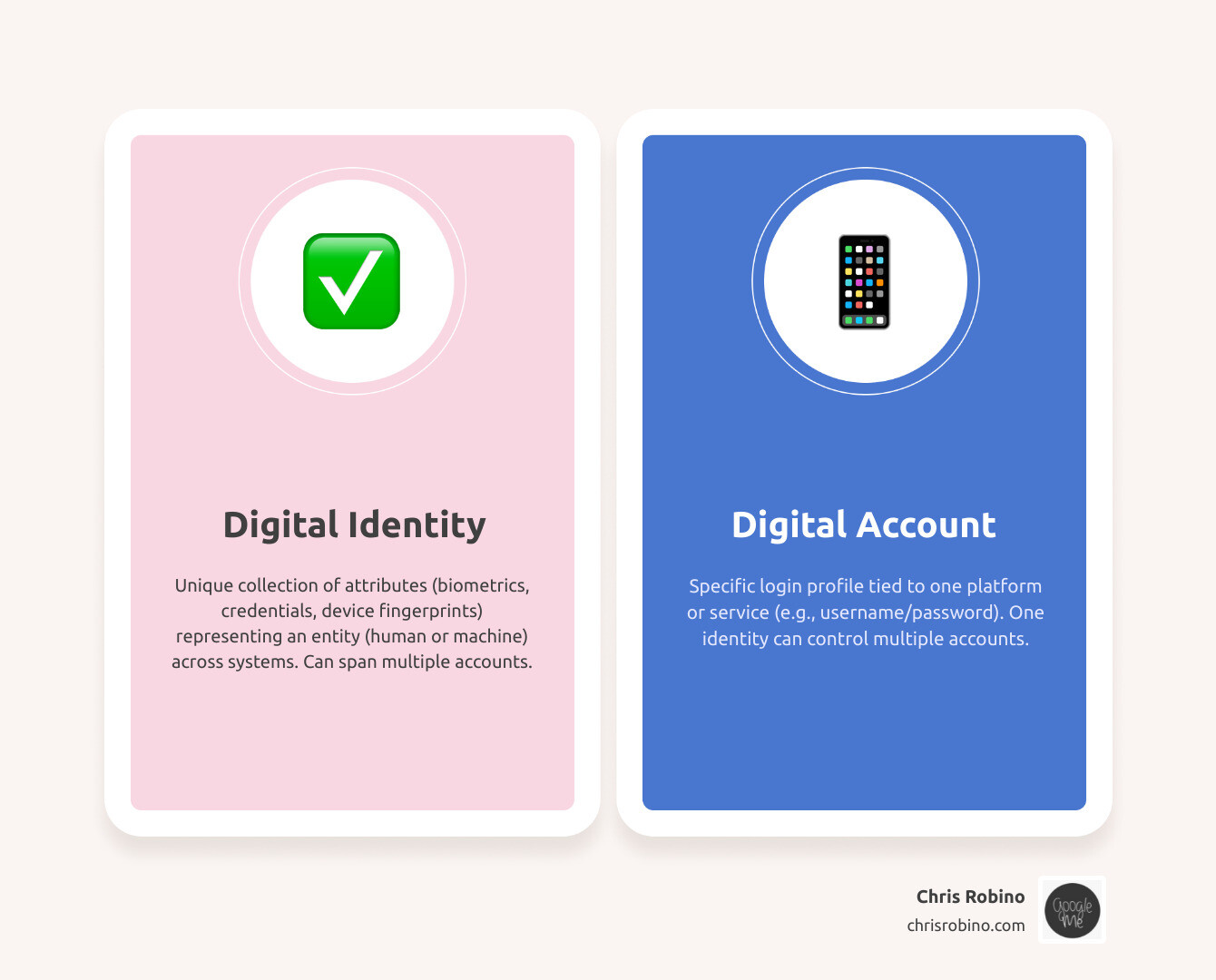
It’s easy to use these terms interchangeably, but in digital identity management, they mean very different things. Understanding these distinctions is vital for technical SEO and site architecture, as it affects how user sessions and permissions are handled at scale.
| Term | Definition | Example |
|---|---|---|
| Digital User | The actual human (or entity) behind the screen. | A Marketing Manager or an external consultant. |
| Digital Identity | The collection of data points (attributes) that represent that user. | A verified email, employee ID, and biometric data. |
| Digital Account | A specific interaction point or “doorway” into a system. | A specific login for the company CRM or HR portal. |
One user has one digital identity but might have five different accounts (Email, CRM, HR portal, Slack, and AWS). Managing this mapping is critical for maintaining a clean data environment.

Authentication vs. Authorization in Digital Identity Management
We often see people get “AuthN” (Authentication) and “AuthO” (Authorization) confused.
- Authentication is the process of proving you are who you say you are. It typically involves verifying credentials such as multi-factor authentication (MFA), biometrics, or cryptographic keys. We strongly recommend MFA for everything; relying on passwords alone is a significant vulnerability.
- Authorization happens after the user is verified. The system checks the permissions associated with that identity. This prevents privilege escalation, where a user tries to gain access to data they aren’t supposed to see. You can read more about the technical nuances in industry-standard guides on authentication and authorization.
Before any of this can happen, we need identity proofing. This is the process of verifying that a person is actually who they claim to be before we issue them a credential. For high-security environments, we look to the NIST SP 800-63a Enrollment and Identity Proofing standards to ensure we aren’t letting imposters into the system from day one.
Managing the Lifecycle of Human and Non-Human Identities
The lifecycle of identities covers everything from a user’s first day at work to the moment they leave.
- User Provisioning: Automatically creating accounts and assigning roles when a new employee joins.
- Maintenance: Updating permissions as the person changes roles within the company.
- Deprovisioning: This is the most critical step. Deprovisioning ensures that when someone leaves the company, their access is revoked immediately across all systems. Leaving “ghost accounts” active is a massive security risk.
But we aren’t just managing humans. Non-human identities (NHIs)—such as machine identities, IoT devices, and service accounts—are exploding in number. For example, an application running on an RDS instance might need to talk to a database. That application needs its own digital identity to do so securely. If we don’t manage these machine identities with the same rigor as human ones, we leave our APIs and cloud infrastructure wide open to attack.
Global Standards and Regulatory Compliance Frameworks
Compliance isn’t just a legal requirement—it’s a trust signal that search engines and customers value. In today’s landscape, digital identity management must align with several heavy-hitting regulations:
- GDPR (General Data Protection Regulation): Focuses on privacy and the “right to be forgotten” for EU citizens. Learn more about GDPR.
- FADP (Federal Act on Data Protection): The Swiss equivalent, which heightens data protection standards.
- HIPAA: Essential for anyone in healthcare to protect patient data. HIPAA details.
- SOX (Sarbanes-Oxley): Critical for financial reporting and auditing. SOX information.
To make these systems work together, we use standards like OAuth (for authorization), OpenID Connect (for authentication), and SAML. These allow for federation, which lets a user use one set of credentials to log into multiple unrelated systems (Single Sign-On). Federation is what makes the modern web feel seamless and secure.
The Future of Digital Identity Management and Organizational Strategy
The “old way” of managing identities—siloed databases and simple passwords—is obsolete. The complexity of modern cloud environments and the rise of sophisticated security threats require a more dynamic, integrated approach. For large companies, this evolution is directly tied to their broader digital and SEO strategies.
As we mentioned, cybercrime in Switzerland increased significantly, largely due to identity-based attacks. Organizations must scale their identity systems to handle millions of identities while maintaining sub-second authentication times to avoid negatively impacting user experience and Core Web Vitals.
One exciting real-world example is the Digital Identity Project by the California Department of Technology. They are building a framework to provide safe and scalable digital access for Californians, moving toward a model where a single digital ID can be used for various state services, reducing friction and increasing security.
Digital Identity as an Enterprise SEO Strategy
For large companies, SEO strategies that perform well are built on a foundation of technical excellence and user trust. Digital identity management plays a surprising but vital role in this:
- Trust and E-E-A-T: Google’s Search Quality Rater Guidelines emphasize Experience, Expertise, Authoritativeness, and Trustworthiness (E-E-A-T). By using robust identity management to verify authors and secure user-generated content, large companies signal to search engines that their platform is a reliable source of information.
- Site Performance and Core Web Vitals: Slow authentication processes can lead to high bounce rates and poor Largest Contentful Paint (LCP) scores. Optimizing the identity layer ensures that security does not come at the cost of speed, which is a critical ranking factor for large-scale websites.
- Security as a Ranking Signal: HTTPS and secure user environments are foundational SEO requirements. A site known for identity breaches will quickly lose its ranking as search engines prioritize the safety of their users.
- Scalable Content Governance: Large companies often manage thousands of pages across multiple subdomains. Centralized identity management allows for secure, scalable content updates, ensuring that only authorized experts can modify high-value SEO assets.
Emerging Technologies in Digital Identity Management
We are entering the era of Identity Fabrics. This is a mesh-like architecture that connects all your identity services into a single, cohesive layer. But that’s just the beginning.
- Artificial Intelligence (AI): AI is now used for “Behavioral Biometrics.” It learns how users interact with systems—their typing rhythm, mouse movements, and typical login times. If someone steals a password but logs in from an unusual location with different behavioral patterns, the AI can flag it instantly.
- Blockchain & Decentralized Identifiers (DIDs): This is the foundation of Self-Sovereign Identity (SSI). Instead of a company “owning” your identity, you own it. You carry your verifiable credentials in a digital eWallet.
- Selective Disclosure: This is a game-changer for privacy. Imagine proving you are over 21 without sharing your name or address. This “privacy-by-design” approach is highly favored by modern data regulations and privacy-conscious consumers.
- Syncable Authenticators: A new focus in the NIST SP 800-63b Authentication and Lifecycle Management guidelines, these allow users to move their passkeys across devices more easily, reducing the “lock-out” frustration that often leads users to bypass security.
Strategic Implementation: In-house vs. Outsourced Models
One of the biggest questions we get at Chris Robino is: “Should we build our own IAM or buy it?”
In-house Digital Identity Management:
- Pros: Total control, deep customization, and data stays on your servers.
- Cons: Extremely expensive, requires rare expert talent, hard to scale, and you are responsible for every security patch. For most large companies, the opportunity cost of building in-house is too high.
Outsourced / Managed Services:
- Pros: Rapid adaptation, lower upfront costs, experts handle the security, and it’s built to scale. This model allows large companies to focus on their core business and SEO strategies while leaving the technical heavy lifting to specialists.
- Cons: Reliance on a third party and potential for “vendor lock-in.”
In regions like Switzerland, the dispatch on the upcoming e-ID Act suggests that a government-backed ID might simplify things for businesses by 2026. However, as noted by industry experts, a number of questions still need to be answered regarding how private companies will integrate with these state systems. For most organizations, a hybrid approach or a managed service is the most logical path forward to combat resource shortages and meet strict FINMA or GDPR auditability requirements.
Conclusion: Securing the Digital Frontier
Digital identity management is no longer a back-office IT task; it is a core business strategy that impacts everything from cybersecurity to enterprise SEO. Whether you are navigating the complexities of the media industry or scaling a global tech platform, your ability to manage identities will determine your security, your user experience, and your regulatory standing.
For large companies, the path to success involves integrating identity management into the broader digital ecosystem. By prioritizing trust, speed, and security, organizations can build a resilient brand that performs well in search results and earns long-term customer loyalty. Strategies that perform well for large companies always put the user’s identity and security at the center of the digital experience.
At ChrisRobino.com, we specialize in helping you make sense of these emerging tech shifts. From digital transformation to streamlined communication, we provide the portal you need to access high-level expertise in a rapidly changing world. We understand that in the digital frontier, identity is the new perimeter, and managing it effectively is the key to unlocking sustainable growth.
The digital frontier is moving fast. Between AI-driven threats and the promise of decentralized identity, the “A to Z” of identity is constantly being rewritten. The key is to stay flexible, stay informed, and always put identity at the center of your security universe.
Ready to take the next step? Get to work with digital transformation for media and let’s build a more secure, identity-centric future together.
